- within Accounting and Audit and Cannabis & Hemp topic(s)
When evaluating a new IT vendor or technology solution, a proof of concept ("POC") is a natural first step. Because a POC is typically short in duration and provided at nil cost, many organisations assume that a simple non-disclosure agreement ("NDA") is sufficient to get started. That assumption is not correct.
An NDA serves an important but narrow purpose: it governs the confidentiality of information shared between the parties. It was never designed to address the full spectrum of risks that arise when a vendor is given access to an organisation's data, systems, or environment. A typical NDA will not address what data the vendor may access and for what purposes, what security standards it must maintain, what happens to the data when the POC concludes, who owns any intellectual property created during the engagement or what liability the vendor bears if something goes wrong. These gaps exist regardless of whether the data in question is personal data, commercially sensitive information or proprietary technical material.
Equally, organisations should not concede on liability simply because a POC carries no fee. The value at risk is not measured by the price paid for the service,it is measured by the potential harm if something goes wrong: a data breach, system downtime, loss of proprietary information, or regulatory exposure. A vendor that introduces risk into your environment should accept meaningful responsibility for that risk, irrespective of cost.
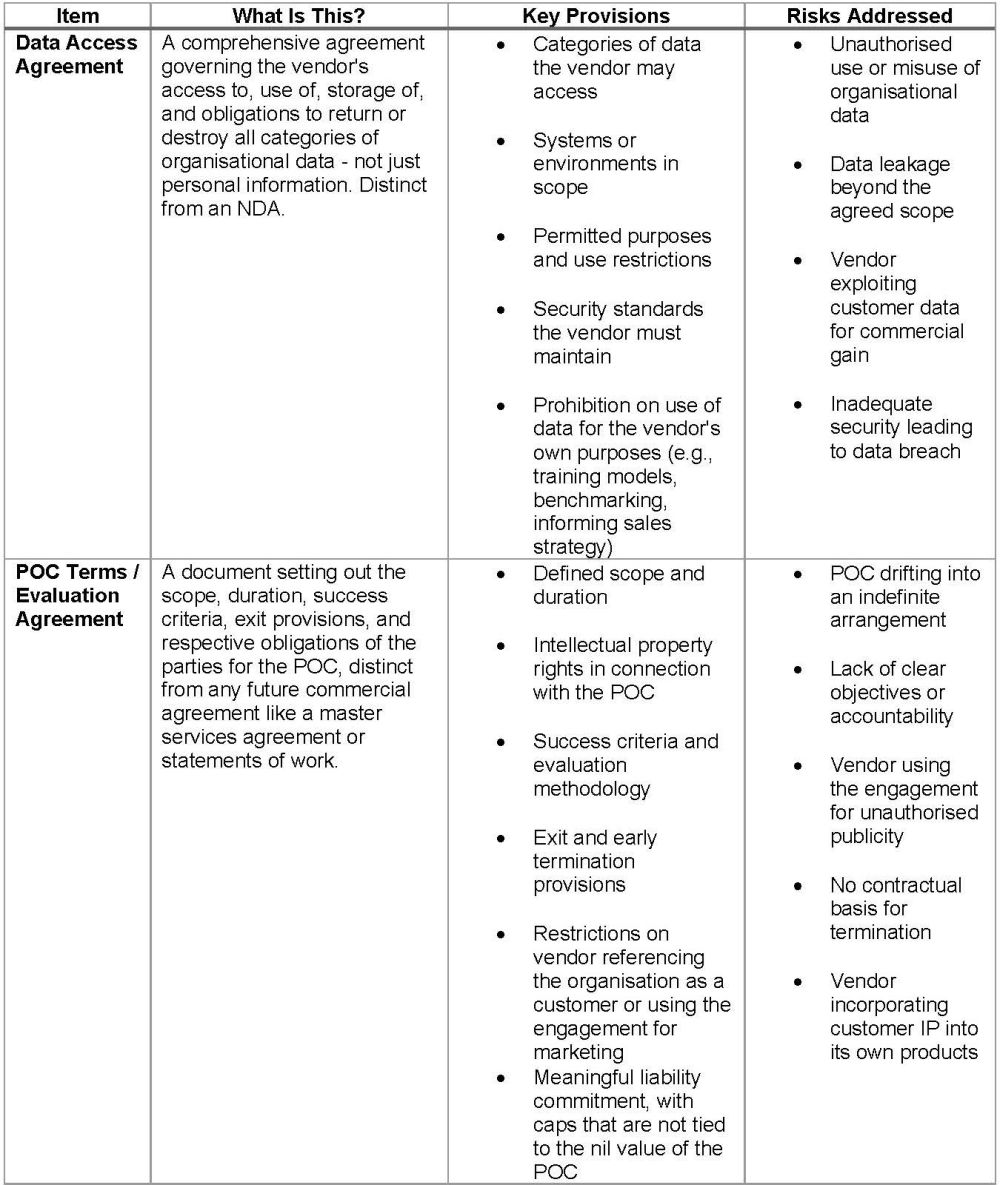
Okay, if an NDA is not enough, then what contractual documents do we need?
The checklist below sets out the key contractual documents that organisations should have in place before any POC commences.
Besides contractual documents, do we need to do anything before the POC?
Having the right contractual documents in place is only part of the picture. Before any data is shared or system access is granted, the organisation should carry out a number of practical due diligence steps to ensure it fully understands the risks of the POC and has the necessary internal approvals in place. This could include:
- Personal Information Impact Assessments: An assessment of the privacy risks associated with the POC, required where personal information will be processed – particularly at scale or involving special personal information.
- Information security assessment: A review of the vendor's security posture and technical and organisational measures to ensure they meet or exceed the organisation's minimum standards.
- Internal stakeholder sign-off: Formal approval from all relevant internal functions before any data is shared or system access is granted.
Once the POC is over, what do we do?
Whether the POC concludes successfully, proves unsuccessful, or is terminated early, the organisation must take prompt action to secure its data and environment. A successful outcome does not mean these steps can be skipped – any continuation of the vendor relationship should be governed by a new commercial agreement, not by the informal carry-over of POC arrangements.
A well-structured POC framework is not disproportionate – it is essential. It protects the organisation against real risks, sets the tone for the vendor relationship, and can serve as a foundation for the full commercial contract should the organisation decide to proceed. The cost of a POC to the customer is never nil; it is the value of the data and systems being put at risk.
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.
[View Source]

