- in Europe
- in Europe
- in Europe
- in Europe
- in Europe
- in Europe
- in Europe
- in Europe
- with readers working within the Law Firm industries
- within Environment and Real Estate and Construction topic(s)
The RBI has given Master Direction on February 18, 20211, which provides necessary guidelines for the regulated entities to set up robust governance structure and implement common minimum standards of security controls for digital payments products and services.
The Master Direction lays down guidelines for the internet banking, mobile payments, card payments, customer protection, and grievance redressal mechanism.
CHANGES IN DIGITAL PAYMENT SYSTEM- ADDING DIGITAL PAYMENT SECURITY CONTROL2
The directions shall be called as Reserve Bank of India (Digital Payment Security Controls) directions, 2021.3 The guidelines are in pursuance to Digital Payments mechanism and the Master Direction paves the way for the Digital Payment Security Controls
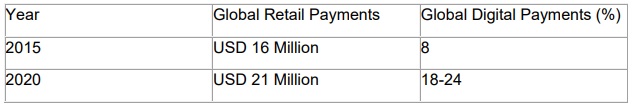
Digital Payment Market Statistics
The Payment landscape4 is seeing heightened activity across multiple player categories ranging from:
- Device Manufacturer
- Technology Firms
- Telecom Companies
- Fintech Startups
STATISTICS5
The regulations shall play a critical role in determining the nature and success of payment solutions. The modernizing of payment infrastructure occurring in most countries, payments service providers can take advantage of the real- time systems to offer cutting edge payment solution to customers.
Existing law6
- The electronic payments were regulated by Payment and Settlement System Act, 2007 ('PSS'), the aim of the PSS Act was to ensure a safe and effectual system of payments and settlement. At the times, transactions were heavily dependent on cash or bank transfer.
- Section 187 - It lays down the policies relating to the regulation of payment systems including which includes electronic, non- electronic, domestic or international payments.
- Section 10 (2)-8 the RBI has the power to determine issue guidelines for the efficient management of payments system.
- The Intermediaries Directions issued by the Reserve Bank of India vide notification dated 24.11.2009.
The Intermediaries Directions regulated the service providers. According to the Directions, banks were required to maintain a nodal account of the intermediaries with permissible credit and debits limit as also the settlement cycle for credit to the merchants. The guidelines were ultimately applicable to Payment Aggregators.
The Directions were applicable to Payment Gateways and Payment Aggregators.
Intermediary Directions are still in force and have not been expressly repealed, having both the Intermediary Directions and Guidelines regulating the digital payment system is only likely to create conflict;
APPLICABILITY OF DIGITAL PAYMENT SECURITY CONTROL
The provisions of these Directions shall be applicable over the following Regulated entities:
- Scheduled Commercial Banks (excluding Regional Rural Banks)
- Small Finance Banks
- Payment Banks
- Credit Card Issuing NBFC
GUIDELINES FOR THE DIGITAL PAYMENTS AND PRODUCTS9
It is put forward by the RBI to improve the security of the digital payment channels, and also convenience for users. The directions contain certain minimum standards on common security controls, for channels like internet, mobile banking and card payments etc.
The basic Tenets of the guidelines by RBI is as follows:
General controls
Registered entities must formulate the policy for the digital payments and products.
The policy must include the payment security requirements from the angles of functionality, security and Performance angles, such as:
Confidentiality of Data
It must protect the confidentiality of customer data and integrity of data.
Backup of Data
The infrastructure such as technology with necessary back up.
Assurance of Payment Product
Assurance that the payment product is built in a secure manner offering robust performance ensuring safety, consistency and rolled out after necessary testing for achieving desired FSP.
High Customer Service
Minimal customer service disruption with high availability of systems/ channels (to have minimal technical declines)
Registered Entities to Formulate policies for the Digital Products and for its payment mechanism
Separate Policy for digital Products- Registered entity must formulate separate policy for its different digital products or include the same as part of their overall product policy. Further, the policy document should require that every digital payment product/ services offered addresses the mechanics, clear definition of starting point, critical intermittent stages/ points and end point in the digital payment cycle, security aspects, validations till the digital payment is settled, clear pictorial representation of digital path and exception handling.
- UTAT-The entities must follow User Acceptance Tests (UAT) in multiple stages before roll out, sign off from multiple stakeholders (post UAT) and data archival requirements shall also be taken in to account.
- Risk Assessment with regard to safety and security of the digital payments products and associated processes and services for the suitability of the target users. The risk assessment should include-
- Technology Bases solutions,
- Vulnerabilities attached to the digital products and remedial action to be taken by the entity
- Checking the dependence on third party service providers
- Tracking the risk arising out of integration of digital payment platform with other systems both internal and external to the RE, which includes core systems and systems of payment systems operators, etc.
- Generic Security Controls
- The secure standard shall be followed for the communication protocol in the digital payment channel. There will be appropriate level of encryption and security in the digital payment ecosystem.
- The web applications providing the digital payments products and services shall not store hidden HTML Cookies, or any other client side storage information.
- The RE shall provide Web Application Firewall solution and DDoS Mitigation techniques to secure digital payment products and services offered over internet.
Application Security Life Cycle (ASLC)
- Multi-Tier Mechanism- There shall be implementation of multi-tier application architecture, which segregates application, database and presentation layer in the digital payment products and services.
- Secure by design -There shall be a system of "secure by design" approach in the development of the digital payments, products or services. The digital payments applications need to be inherently secure by embedding security within their application.
- Security Objectives-Registered Entities shall explicitly define security objectives (including protection of customer information/ data) during:
(a) Requirements gathering, (b) designing, (c) development, (d) testing including source code review, (e) implementation, maintenance & monitoring and (f) decommissioning phases of the digital payment applications.
- 1. Escrow Account in case of Third Party Vendors -For digital payment applications that are licensed by a third party vendor, Registered Entities shall have an escrow arrangement for the source code for ensuring continuity of services in case the vendor defaults or is unable to provide services.
- 2. Security Testing- REs shall conduct security testing including review of source code, Vulnerability Assessment (VA) and Penetration Testing (PT) of their digital payment applications to assure that the application is secure for putting through transactions while preserving confidentiality and integrity of the data that is stored and transmitted.
- 3. Authentication Framework
The increased medium of "electronic mode of transfer", for this the notification of RBI has professed that Registered Entity must follow the multifactor authentication system in order to break off the cyber-attacks.
- Fraud Risk Management
- Configuration of suspicion- The registered entities must document the configuration aspect identifying the suspicious transactional behavior and implement the respective rules detective types of control, mechanism to alert the customer in case of failed authentication.
- System Alerts- The system alerts shall be parametrized and monitored in terms of applicable parameters. Such parameters are transaction velocity, (E.g.-fund transfers, cash withdrawals, payments through electronic modes, adding new beneficiaries, etc.) in a short period, more so in the accounts of customers who've never used mobile app/ internet banking/ card ever (depending upon the type of payment channel), high risk merchant category codes (MCC) parameters, counterfeit card parameters (String of Invalid CVV/ PINs indicates an account generation attack), new account parameters (excessive activity on a new account), time zones, geo-locations, IP address origin (in respect of unusual patterns, prohibited zones/ rogue IPs), behavioral biometrics, transaction origination from point of compromise, transactions to mobile wallets/ mobile numbers/ VPAs on whom vishing fraud or other types of fraud is/are registered/ recorded, declined transactions, transactions with no approval code, etc.
- Customer Protection, Awareness, and Grievance Redressal Mechanism
- Guidelines and Training Materials -Registered Entities shall incorporate secure, safe and responsible usage guidelines and training materials for end users within the digital payment applications. They shall also make it mandatory (i.e. not providing any option to circumvent/ avoid the material) for the consumer to go through secure usage guidelines (even in the consumer's preferred language) while obtaining and recording confirmation during the on-boarding procedure in the first instance and first use after each update of the digital payment application or after major updates to secure and safe usage guidelines.
- Lodge Customer Grievance- Registered Entities shall incorporate a section on the digital payment application clearly specifying the process and procedure (with forms/ contact information, etc.) to lodge consumer grievances. The reporting facility on the application shall provide an option for registering a grievance. Customer dispute handling, reporting and resolution procedures, including the expected timelines for the RE's response should be clearly defined.
- Internet Banking Security Controls
- Additional Level of Authentication- Internet banking websites are vulnerable to authentication related brute force attacks/ application layer Denial of Service (DoS) attacks. Based on the RE's individual risk/ vulnerability assessment on authentication-related attacks such as brute force/ DoS attacks, REs shall implement additional levels of authentication to internet banking website such as adaptive authentication, strong CAPTCHA (preferably with anti-bot features) with server-side validation, etc., in order to plug this vulnerability and prevent its exploitation. Appropriate measures shall be taken to prevent DNS cache poisoning attacks and for secure handling of cookies. Virtual keyboard option should be made available
- Mobile Payment Application Control
Specific Controls for mobile applications include:
- Device policy enforcement (allowing app installation/ execution after baseline requirements are met);
- Application secure download/ install;
- Deactivating older application versions in a phased but time bound manner (not exceeding six months from the date of release of newer version) i.e., maintaining only one version (excluding the overlap period while phasing out older version) of the mobile application on a platform/ operating system;
- Storage of customer data;
- Card Payment Security
Payment Card Standards- Registered Entity shall follow various payment card standards (over and above PCI-DSS and PA-DSS) as per Payment Card Industry (PCI) prescriptions for comprehensive payment card security as per applicability of updated versions of the standards such as -
- PCI-PIN (secure management, processing, and transmission of personal identification number (PIN) data);
- PCI-PTS (security approval framework addresses the logical and/ or physical protection of cardholder and other sensitive data at point of interaction (POI) devices and hardware security modules (HSMs);
- PCI-HSM (securing cardholder-authentication applications and processes including key generation, key injection, PIN verification, secure encryption algorithm, etc.); and
- PCI-P2PE (security standard that requires payment card information to be encrypted instantly upon its initial swipe and then securely transferred directly to the payment processor).
Conclusion
In view of the proliferation of cyber-attacks and their potential consequences, REs should implement, except where explicitly permitted/ relaxed, multi-factor authentication for payments through electronic modes and fund transfers, including cash withdrawals from ATMs/ micro-ATMs/ business correspondents, through digital payment applications. At least one of the authentication methodologies should be generally dynamic or non-replicable. [e.g., Use of One Time Password, mobile devices (device binding and SIM), biometric/ PKI/ hardware tokens, EMV chip card (for Card Present Transactions) with server-side verification could be termed either in dynamic or non-replicable methodologies.].
Footnotes
1 https://www.rbi.org.in/scripts/NotificationUser.aspx?Id=12032&Mode=0
2 https://www.rbi.org.in/scripts/NotificationUser.aspx?Id=12032&Mode=0
3 https://www.rbi.org.in/scripts/NotificationUser.aspx?Id=12032&Mode=0
4 https://image-src.bcg.com/BCG_COM/BCG-Google%20Digital%20Payments%202020-July%202016_tcm21-39245.pdf
5 https://image-src.bcg.com/BCG_COM/BCG-Google%20Digital%20Payments%202020-July%202016_tcm21-39245.pdf
7 https://indiankanoon.org/doc/126521356/
9 https://www.rbi.org.in/scripts/NotificationUser.aspx?Id=12032&Mode=0
For further information please contact at S.S Rana & Co. email: info@ssrana.in or call at (+91- 11 4012 3000). Our website can be accessed at www.ssrana.in
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.


