As of the effectiveness date (June 1st,2017) of the Cybersecurity Law of PRC.,China has promulgated many new regulations and rules on personal data protection. On May 1st, 2018, the national standard of the "Information security technology—Personal information security specification" (the "Standard") has also become effective. The Regulations for the Security Protection of Critical Information Infrastructure ("Regulation") is currently in the process of legislation and will be promulgated soon. We recently advised several international institutions on their online whistleblowing and personal information protection relatedissues and below are some main points which are worth to be noted and discussed.
1. Online Whistleblowing system and Personal Information Protection
The online whistleblowing system enables the employees in private enterprises, government agencies or other institutions to disclose to the public or the competent authority or person of mismanagement, corruption, illegality, or some other wrongdoing by online platform or other online system. Below are two whistleblowing routes involved:
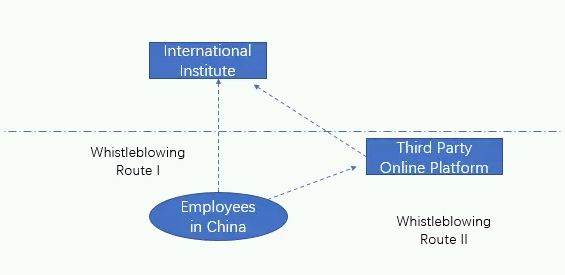
Under Whistleblowing Route I, the employees in China will disclose information directly to certain person or authority in the international institute directly. Under Whistleblowing Route II, the international institute will enter into an agreement with the third party online platform, who will provide whistleblowing related services. In order to comply with Chinese laws, certain issues should be considered such as critical information infrastructure, personal information and cross-boarder transfer of personal data.
2. Whether the international institute and third party online platformare deemed as an operator of critical information infrastructure
Underthe Cybersecurity Law, online operators are categorized into two types: critical information infrastructure ("CII") operator and non-CII operators. CII operators will have higher level responsibilities on personal information protection. For instance, the CII operator will store within China any personal information and important data collected and generated during its operation within China. Where such information and data have to be provided abroad for business purpose, security assessment shall be conducted pursuant to the laws.
The Cybersecurity Law defines CII operating in
important industries and sectors such as public communications,
information service, energy, transport, waterconservancy, finance,
public service and e-government, and other critical information
infrastructure that, once damaged, disabled ordata disclosed, may
severely threaten the national security, national economy,
people's livelihood and public interests. Pursuant to the
Regulation, the network facilities and information systems operated
and administered by the following entities shall be included in the
scope of critical information infrastructure as their
damage,dysfunction or data leakage may severely jeopardize national
security, people's livelihood and public interest:
(1) government agencies and entities in the energy, finance,
transportation, water conservation, health care, education, social
insurance, environmental protection and public utilities
sector;
(2) information networks,such as telecommunication networks,
broadcast television networks and the internet, and entities
providing cloud computing, big data and other large-scale public
information network services;
(3) research and manufacturing entities in sectors such as science
and technology for national defense, large equipment manufacturing,
chemical industry and food and drug sectors;
(4) press units such asbroadcasting stations, television stations
and news agencies;
(5) other key entities.
Thus, it will be important to analyze whether the international institute and third party online platform are deemed as an operator of critical information infrastructure herein. TheCybersecurity Law does not limit the operator of CII to be a Chinese entity although theCybersecurity Law is applicable to the construction, operation, maintenance, and use of networks, as well as to cybersecurity supervision and management within the mainland territory of China. If the international institute and third party online platform constitute operators of CII, they will be subject to higher degree of responsibilities on cybersecurity and personal information protection.
3. Personal Information Protection and Cross-border Transfer of Personal Data
The "Measures for the Security Assessment of Personal Information and Important Data to be Transmitted Abroad ( Exposure Draft ) " ( the "Measures" ) defines personal information to be all kinds of information recordedby electronic or other means that can be used to independently identify or be combined with other information to identify natural persons' personal information including but not limited to: natural persons' names, dates of birth, ID numbers, biologically identified personal information, addresses and telephone numbers, etc.
The Standard defines the following personal information as personal sensitive information, including ID number, personal biological identification information, bank account, telecommunication recordsand contents, asset information, credit information, tractinformation, accommodation information, health and physiology information, transaction information, personal information of children under 14 years old, etc. The storage and transmission of personal sensitive information will be required to take security measures such as encryption.
In respect of the transmission of personal information abroad, the network operator (whether CII operator or not) shall provide an explanation on the purpose, scope, content and receiver of the data to be transmitted abroad, and the country or region where the receiver is located to the owner of the personal information, and the transmission shall be consented by such owners. Outbound transmission of personal information of a minor shall be agreed by the guardian thereof.
The transmission abroad of both personal information and important data[1] generated or collected by a network operator during its operation within the territory of China will be subject to security assessment under the Measures. Under the following circumstances, a network operator shall apply to its industrial authority or regulator to organize security assessment:
(1) The data to be transmitted abroad contains or contains in
aggregate the personal information of morethan 500,000
users;
(2) The quantity of the data to be transmittedabroad is more than
1,000 gigabytes;
(3) The data to be transmitted abroad contains data in the areas of
nuclear facilities, chemical biology, defense industry, population
and health, as well as the dataof large-scale project activities,
marine environment and sensitive geographic information;
(4) The data to be transmitted abroad contains system
vulnerabilities, security protection and other network security
information of critical information infrastructures;
(5) A critical information infrastructure operator provides
personal information and important data abroad;
(6) Other data which may affect national security, and social and
public interests, and are necessary for assessment as determined by
the industrial authority or regulator. Otherwise, the security
assessment can be done by the entity on its own.
During the security assessment for the data to be transmitted
abroad, the following aspects shall be highlighted:
(1) necessity of transmittingthe data abroad;
(2) personal information involved, including the quantity, scope,
type and sensitivity of personal information, as well as whether
the owner of personal information agrees to transmit his personal
information abroad;
(3) important data involved,including the quantity, scope, type and
sensitivity of important data;
(4) security protection measures, ability and proficiency ofthe
data receiver, as well as the network security environment of
thecountry or region where the date receiver is
located;
(5) risks of leakage, damage, alteration and abuse of data after
being transmitted abroad and further transferred;
(6) risks to national security,social and public interests, and
personal legitimate interests arising from transmitting the data
abroad and gathering the data to be transmitted abroad;
(7) other important matters to be assessed.
However, any personal information or important data shall not be
transmitted abroad in any of the following
circumstances:
(1) the outbound transmission fails to be approved by the owner of
personal information, or may jeopardize personal
interests;
(2) the outbound transmission causes security risks to the
nation's politics, economy, technology and defense, which may
affect national security and jeopardize social and public
interests;
(3) other data which are forbidden to be transmitted abroad as
determined by the state cyberspace administration , public security
authority, security authority and other relevant authorities.
Under the whistleblowing scenario, when the employees make information disclosure in the anonymous or identified manner, personal information may be involved and proper personal information protection measures should be taken. In respect of personal sensitive information, security measures such as encryption should be taken inrespect of the storage and transmission. When it comes to cross-border transmission of personal information, security assessment should be conducted either by the network operator itself or by the competent authority. The time for storage of personal information should be minimized and any personal information should be de-identified immediately after the collection and be separately stored from other personal information which could be recovered for identification purpose. The network operators should, in light of its business development and network operation, conduct security assessment of the data to be transmitted abroad from time to time (at least once a year) and sufficient internal control policies and data export security assessment mechanisms should be established.
Footnote
1 The Measures defines important data to be the data closely related to national security, economic development and public interests, and the relevant national standards and guidelines for identification of important data shall apply mutatis mutandis to the specific scope of important data.
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.

