The agility of cloud-based security analytics platforming can serve as a catalyst to enable security analytics and security event management. Commoditized operating expense (OpEx) – based pricing and low capitalization costs are additional factors that allow for a consumption model that grants real-time experience that can drive changes in business behavior while leveraging technology to make strategic, data-driven decisions.
A handful of simple transaction situations grouped together in real-time would allow a firm to make inferences about connected security-related events and misconfigurations. Typical outcomes from these near real-time analyses allow for a quick response that can enable bespoke security measures to be enacted.
Previously, an analysis of this level and volume of historical data would take days to perform, but it now takes a few minutes through cloud-based analytics. Such analytics can empower security staff and business leaders to make changes in behavior faster than ever, even when security risks are constantly changing. As a result, the staff can increase their speed in responding to unforeseen events.
As storage of data analytics becomes more commoditized, that level of pricing allows for longer and deeper analytics storyboards than was previously possible and can be retained in a cost-efficient manner for multiple years.
With the power of data and analytics, security staff can now employ analytics scenarios within a few hours instead of weeks. This immediate access to information on the outcomes of financial execution scenarios enables an acutely surgical approach to financial systems security analytics and analysis.
This case study of analysis, design, and build will help illustrate the catalytic impact of cloud-based agility for real-time security analytics.
Making Agile Decisions in Financial Services
A large financial organization that processes monetary transactions uses security data analytics in the Cloud to discover key signatures in both real-time and historical analysis.
The organization had previously leveraged a private on-premises computing environment to perform historical analysis of trade execution data, and that analysis could be used to gain insight into future trade executions. Attaining these results using a cloud consumption model allowed for a highly agile, iterative approach to making multi-system related corrections that leverage near-real-time analyses.
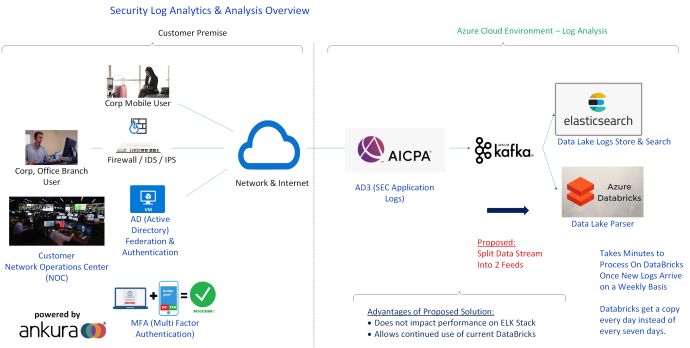
Ankura partnered with the financial company to design and implement two parallel security analytics processing platforms. The solution leveraged Kafka to ingest logs into searchable and extensible Elasticsearch for security analytics queries and alerts and Azure Databricks relational database for historical analysis.
Figure 1: Financial Firm's Custom, Multi-Pipeline Real-Time Cloud Security Analytics Platform
Now, the broader finance department has access to information and data that was only available to senior finance staff members. For this enterprise, consumption of financial security reporting is now as easy as grabbing a cup of coffee compared to previous methods that required large capital investments and specialized, traditional IT services.
A change in behavior brought about by the catalytic effect of cost-effective cloud computing led to broad access of previously scarce computing resources. With cloud-based delivery of analytics, the finance staff at this organization views IT as a strategic partner and has brought IT professionals into its strategy discussions on future financial platforms.
Advisory Recommendations
This scenario highlights the ability of cloud-based security analytics enabling companies to be agile in how they consume security services near real-time analytics needs based on their business cycle. That agile consumption ability delivers significant competitive advantages.
Ankura: How We Can Engage, Advise, Implement & Provide Value
Our ability to listen, assess as well as design and implement cloud security services can immediately add operational value. We pride ourselves in understanding our customers first and then designing cloud services with a hybrid approach including the implementation of security and real-time threat analytics systems available on-demand that can scale up and down in the cloud to minimize the cost of adoption. It can start with a conversation and a proof-of-value engagement that lets our clients determine what's best for their business.
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.

