- within Media, Telecoms, IT and Entertainment topic(s)
As reported by the Wall Street Journal and cybersecurity firms Kaspersky Labs, Sophos, and others, hackers and nation-state actors have recently used rising fears about the coronavirus (COVID-19) to lure individuals and corporate employees into phishing scams. Given the headlines and public concern over COVID-19, it is critical that businesses' IT and security teams—and their employees—be on high alert.
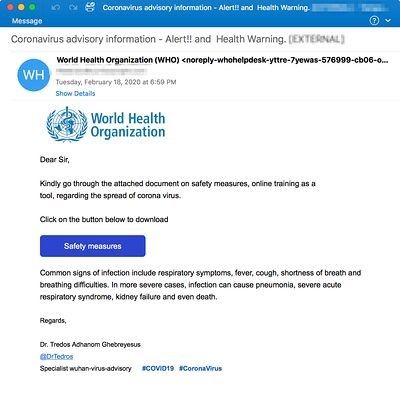
For example, phishing emails have come from spoofed World Health Organization (WHO) email addresses as pictured below:
In addition, hackers have attempted to gain access to networks by sending scam emails with at least one of the following five strategies:
- Phishing emails with fake purchase orders for face masks and other supplies sent as attachments in Word format.
- Phishing emails designed to stoke fears of an available cure that is being withheld and a fake DocuSign page encouraging recipients to share personal credentials to obtain more information.
- Phishing emails asking for employee login information to set up remote worksites.
- Phishing emails from spoofed healthcare providers with malicious attachments.
- Phishing emails cryptically titled "NOTIFICATION" which purport to be sent by disability welfare service providers which request the recipient read a malicious attachment.
It is very likely that hackers are using many other COVID-19 related strategies for usurping standard security protocols. Given the anxiety-riddled atmosphere surrounding COVID-19, organizations should immediately take precautionary measures to reinforce employee cybersecurity practices, including the implementation of a "Report Phishing" email functionality, if possible.
The Buchanan Cybersecurity and Data Privacy team is experienced in helping clients prepare for and—if necessary—respond quickly to cyberscams and other threats to data security.
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.
[View Source]



