- with readers working within the Retail & Leisure industries
Following the release of the Guidelines for Cybersecurity Standards Practices - Security Certification Specifications for Cross-Border Processing of Personal Information (《网络安全标准实践指南— —个人信息跨境处理活动安全认证规范》in Chinese) on June 24, 2022, and the Provisions on Standard Contract for Cross-border Transfer of Personal Information (Draft for Comments) (《个人 信息出境标准合同规定(征求意见稿)》in Chinese) along with the Standard Contract for Crossborder Transfer of Personal Information ("Standard Contract") on June 30, 2022, the Cyberspace Administration of China ("CAC") formally issued the Measures for the Security Assessment of Data Cross-border Transfer (《数据出境安全评估办法》in Chinese, "Assessment Measures") at long last on July 7, 2022, following its draft published on October 29, 2021.
The Assessment Measures will come into force on September 1, 2022, the first anniversary of the implementation of the Data Security Law of the People's Republic of China. With less than two months left, it is highly recommended that the relevant enterprises should evaluate the application of the security assessment and get well prepared for its implementation, if necessary.
Notably, if the data export activities that have been carried out before the implementation of the Assessment Measures do not conform to the provisions thereunder, rectification shall be completed within 6 months from September 1, 2022.
This alert will introduce the Assessment Measures from a practical perspective for reference by enterprises, especially multinationals, with the needs for cross-border transfer of important data and a large amount of personal information.
I. Application Scope
The Assessment Measures largely maintains the substantive provisions regarding the application scope in its draft, with further clarification on the thresholds for personal information.
Specifically, on the one hand, the following two types of data handlers shall always apply for security assessment when providing overseas important data and/or personal information collected and generated in the course of operations within the territory of mainland China (hereinafter, "China", excluding Hong Kong, Macau and Taiwan):
- critical information infrastructure operators ("CIIOs"); and
- personal information handlers that have processed personal information of more than 1 million individuals.
On the other hand, for non-CIIOs that have processed personal information of less than 1 million individuals, security assessment shall also be applied for if any of the following conditions is met:
- providing important data abroad;
- providing personal information of more than 100,000 individuals accumulatively since January 1st of the preceding year abroad; or
- providing sensitive personal information of more than 10,000 individuals accumulatively since January 1st of the preceding year abroad.
Such application scope corresponds to that of the Standard Contract. That means, for non-CIIOs that have processed personal information of less than 1 million individuals, if none of the above conditions is met, the approach of Standard Contract could be adopted for cross-border transfer of personal information, without the need to apply for security assessment. Otherwise, security assessment will be triggered.
II. Self-assessment
Before applying for security assessment, a self-assessment of the risks of data export shall be conducted first, focusing on the following aspects:
- the legality, legitimacy, and necessity of the purpose, scope, and method of data export and of the processing activities of overseas recipient;
- the amount, scope, type and sensitivity of the data to be exported, the risks that the data export may pose to national security, public interest, and the legitimate rights and interests of individuals or organizations;
- whether the responsibility and obligations undertaken by the overseas recipient, as well as its management and technical measures and capacity to fulfill the responsibility and obligations can ensure the security of the data to be exported;
- the risks of data being tampered with, destroyed, leaked, lost, transferred, or illegally obtained or used during or after data export, and whether the channels for individuals to exercise the rights and interests of personal information are available, etc.;
- whether the data export related contract or other documents with legal force (collectively, "legal document") to be concluded with the overseas recipient fully specifies data security protection responsibilities and obligations; and
- other matters that may affect the security of data export.
III. Application for Security Assessment
According to the Assessment Measures, the following materials shall be submitted for the application for security assessment:
- a written application;
- the report of self-assessment on the risks of data export;
- the legal document to be concluded between the data handler and the overseas recipient; and
- other materials required for the security assessment.
It is unclear what shall be included in the written application. We understand that a template may be issued by the competent authorities next for efficiency. With respect to the report of self-assessment, for personal information export, it is supposed that the report of personal information protection impact assessment could be submitted instead.
As for the legal document, the Assessment Measures requires that at least the following matters shall be included:
- the purpose, method and scope of data export, the purpose and method of data processing by the overseas recipient;
- the location and duration of data storage outside China, as well as the measures to handle the data exported after the retention period expires, the agreed purpose is completed, or the contract is terminated;
- the binding provisions that restrict the overseas recipient from transferring the exported data to other organizations or individuals;
- the security measures that the overseas recipient should take in the event of substantial changes in actual control or scope of business, or changes in the data protection related policies and regulations and cybersecurity environment of its country or region, or other occurrence of force majeure that make it difficult to ensure data security;
- the remedies, liabilities and dispute resolution for breach of data security protection obligations agreed in the legal document; and
- the requirements for proper emergency response and the ways and methods for individuals to protect their personal information rights and interest, when the data exported is at risk of being tampered with, destroyed, leaked, lost, transferred, or illegally obtained or used.
In absence of further clarification, it is supposed that, for personal information export, the Standard Contract could be used as the "legal document" to be submitted for security assessment.
IV. Assessment Authority and Timeframe
Security assessment shall be applied to the CAC through the local cyberspace administration ("CA") at the provincial level. The procedure and timeframe of security assessment is as below.
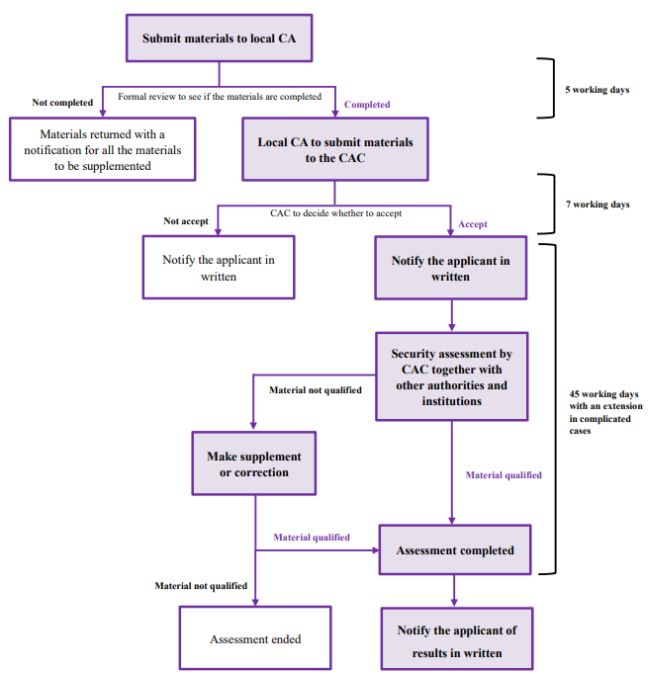
In addition, if the data handler has any objection to the assessment results, it can apply to the CAC for re-assessment within 15 working days upon receiving the assessment results, and the reassessment results will be the final decision.
V. Security Assessment
Article 8 of the Assessment Measures provides the focuses of the security assessment. In particular, the matters to be assessed in security assessment by CAC overlap with the matters of risk selfassessment to a large extent. The former mainly increases the assessment of the impact on the security of data exported of the data security protection policies and regulations and the cybersecurity environment of the country or region where the overseas recipient is located, as well as the assessment of compliance with Chinese laws, administrative regulations and departmental rules.
VI. Expiration and Re-assessment
Subject to the Assessment Measures, the assessment results will only be valid for 2 years. If it is necessary to continue the original data export activities after the expiration of the validity period, the data handler shall apply the assessment again 60 working days before the expiration. Otherwise, the data export activities shall be ceased.
Besides, during the period of validity, if there is a substantive change in data export (such as changes in the purpose, scope, method of data processing; the retention period, etc.); or there is a change in overseas laws and policies and cybersecurity environment, or in actual control of data handler and overseas recipient, that affect data security; or other circumstances that affect the security of the data exported occur, the security assessment shall be re-applied for.
VII. Looking Forward
Recently, China has intensively issued regulations and documents concerning cross-border data transfer. With the release of the guidance for certification, the draft Standard Contract and the Assessment Measures in succession, China's cross-border data transfer regime is entering into a new stage.
For enterprises, the long-standing uncertainty in this regard since the promulgation of the Personal Information Protection Law of the People's Republic of China and the Data Security Law of the People's Republic of China is being resolved, but meanwhile, great challenges are to be faced in terms of compliance work and business arrangements.
It is recommended that the relevant enterprises shall conduct a comprehensive assessment of the status quo of data export during the two-month grace period, so as to get well prepared for the implementation of the Assessment Measures. For those that do not need to apply for the security assessment, other approaches could be considered if required, as the certification mainly for intragroup transfer is close to operation, and the Standard Contact is expected to be formally issued very soon.
Click here to continue reading...
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.



