- within Environment topic(s)
Recent high profile events such as the 'WannaCry' and 'Petya' Ransomware attacks have highlighted the very significant exposure security incidents pose for organisations and the legal and commercial challenges that can follow. The implementation of Australia's Data Notification Law is likely to further increase the exposure of affected organisations to costs associated with security incidents and events that follow a breach.
Australia's Federal Parliament has now passed the Privacy Amendment (Notifiable Data Breaches) Act 2017 (Cth) (Data Notification Law) which will take effect from 22 February 2018 and impose new obligations by amending Australia's existing Privacy Act 1988 (Cth) (Privacy Act). To view our recent summary of the new laws, please click here.
To provide guidance on how Australian organisations are likely to be affected by Australia's Data Notification Law and security risks generally, Clyde & Co has drawn on its international experience in managing cyber claims and data breaches to prepare our second annual cyber report that explores the key aspects of the legislation, as well as a detailed analysis of a cross section of breaches that we have worked on across various industries to provide insight into the likely costs and consequences of the new regime.
A snapshot of our analysis of the financial costs of data breaches which includes graphs, trends and cost breakdowns can be downloaded here.
To request a copy of our second annual cyber report, which also includes key recommendations on steps organisations should take in preparation for 22 February 2018, please click here.
The Data Set
Clyde & Co has also performed a detailed analysis of breach costs and sector risks based on an initial data set of 70 separate global breaches. The majority of these matters were US based data breaches (though some also had international exposure), as well as five separate Australian breaches, and two Asian breaches. This initial data set was refined, with the following matters removed:
- Pure ransom and crypto-locker events, unless these incidents also involved evidence of data exfiltration. This was done because the costs incurred in pure ransomware events generally consist of the ransom payment (where it was determined it was appropriate to pay the ransom) or forensic and investigation costs associated with data restoration. Generally speaking these claims were the simplest matters observed and were the most quickly resolved;
- Suspected incidents, where following investigations it was determined no personally identifiable information had been disclosed or stolen. These matters typically only involved limited forensic and legal costs and generally speaking the matters were resolved within three months; and
- Claims for business interruption loss. 1 These claims had not been made in every case, however in some of the matters business interruption losses of over USD 1 million had been alleged.
Matters Per Industry
Following these revisions, 30 separate data breaches were identified and used for our analysis. These breaches fell into the following industries:
- Healthcare - made up of organisations including large hospital networks, individual clinics, smaller practices and specialised testing and diagnostic services;
- Retail and hospitality - which included retail shops, restaurants, online stores and accommodation service providers;
- Professional services - including financial service firms as well as risk and investigation firms; 2
- Computer hardware - a hardware manufacturer; and
- Utilities - a government related entity.
It was noted that the highest concentration of matters was in the healthcare sector which reflects recent commentary that healthcare information is being increasingly used to commit both financial and identity fraud and the underlying sensitivity individuals feel where their medical records and information are compromised.
Sensitivity around healthcare information breaches is also likely to be seen in Australia given 79% of respondents recently surveyed by the OAIC indicated they placed very high level of trust in their health service providers. 3
The second most significant category was hospitality & retail which involved a variety of point of sale attacks, social engineering attacks and some unintended unauthorised disclosures. A number of these matters became high profile breaches receiving significant media attention.
Costs by Category
Across all of the matters considered, the analysis showed that the various costs that were incurred and proportion of each cost were as follows:
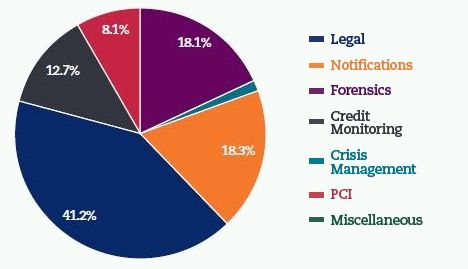
- Forensics (18.11%) The cost of IT and security experts retained by the organisation to investigate the incidents and provide ongoing advice on the management of each breach. These costs did not include any hardening or remedial work that was undertaken after the breach had been remedied to improve the overall security environment of the organisation;
- Crisis Management (1.7%) Costs of obtaining an independent crisis expert and costs associated with public relations and ongoing communications advice. These costs represented an insignificant percentage across all of the matters;
- Notification (18.3%) Costs in identifying, preparing and providing notification correspondence to affected individuals of disclosure incidents. These costs include the provision of call centre services and any complaint mechanisms that are provided as part of these call centre services;
- Legal (41.2%) Made up of privacy counsel, 4 regulatory legal costs, 5 defence Costs, 6 investigations costs, 7 and legal costs associated with the Payment Card Industry Data Security Standards (PCI DSS);
- Credit Monitoring (12.7%) Costs incurred to provide mitigation tools to affected individuals in the form of access to credit monitoring services and other identity protection services;
- Payment Card Industry (PCI) (8.1%) Costs incurred under the PCI DSS regime which imposes obligations to obtain a PCI forensic investigator (PFI), compliance penalties and assessments representing the losses incurred by financial institutions to remediate breaches that compromise individuals' payment cards and financial records; and
- Other (0.0%) Miscellaneous direct costs flowing from a breach.
Across our data the highest cost incurred was legal, although this reflects the complexity of managing privacy and data notification obligations, as well as the relatively sophisticated regulatory and plaintiff litigation environment that has evolved in jurisdictions such as the US. It is not anticipated these trends will be immediately experienced in Australia and adjustments have been made in the graphs below to reflect the more likely outcomes we anticipate will be experienced once the Data Notification Law comes into force.
The statistics above show that 31% of the total costs incurred were for notification and credit monitoring. While there are significant variations across industries this figure shows that managing notification and providing mitigation services to affected individuals is a key cost to incident response and should be carefully considered by organisations prior to February 2018 when the Data Notification Law comes into force.
The cost of forensics was also relatively low in percentage terms however this was influenced by a number of the matters in the data set that were breaches of high profile organisations with established internal information technology teams that helped perform forensic and investigation steps post breach. Where breaches involve smaller and mid-level organisations the percentage cost of forensic services increased.
Costs Over Time
A number of commentators have described data breach incidents as short tail risks which generally resolve in the months following incidents. This is not supported by the data which reveals costs can continue to be incurred 25 months after the initial incident occurred.
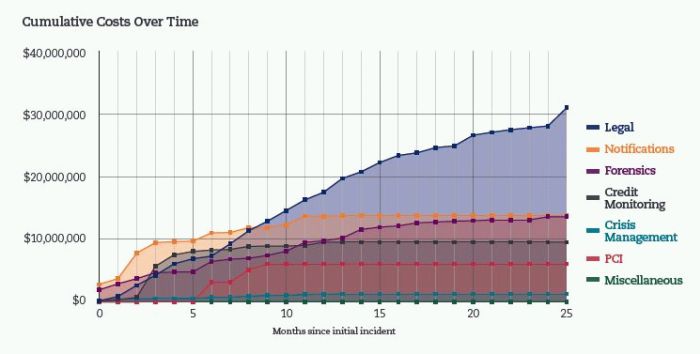
The most significant cost observed during the first five month period was for notification and credit monitoring. Additional expenses were incurred for these items in situations where additional affected individuals were identified at later periods and other forms of notification were required to reach subsets of affected individuals (including examples where it became difficult to determine proper contact details and further steps were required). In these matters, notification was almost exclusively provided by way of registered mail. This is not strictly a requirement under Australia's Data Notification Law.
In general credit monitoring costs were incurred to provide credit and identity protection support to individuals whose records had been compromised. In a number of cases credit monitoring services were initially based on single credit bureau services, however, depending on the sensitivity of the records compromised, additional services were also provided. Some credit monitoring costs stemmed from disputes around the adequacy of the credit monitoring initially offered to affected individuals. Many of the services provided were bulk products with the product cost set based on presumed levels of take up from impacted individuals.
Footnotes
1. Business interruption is typically the consequential
loss incurred by the organisation as a direct result of the
incident or suspected incident. Business interruption losses are
typically covered under cyber insurance policies, though there is
significant variation between individual policy wordings around the
triggers for cover and waiting and excess periods.
2. The wider data set also included a number of other professional
service companies such as legal services and accounting firms.
However these matters were pure ransomware events and were excluded
based on the criteria summarised above.
3. Office of the Australian Information Commissioner, Australian
Community Attitudes to Privacy Survey 2017 (May 2017)
4. These are the solicitors that are retained at an initial stage
to determine whether or not privacy or data notification
obligations will arise as a result of the incident.
5. These are the costs associated with managing and defending any
steps taken by regulators as a result of a data breach
incident.
6. These are the costs incurred to defend third party litigations
brought against a company following a security incident. Typically
these actions are brought by affected individuals, third party
clients or financial institutions. These types of claims are
discussed further in Matthew Pokarier and Benjamin Di Marco, Clyde
& Co, Emerging legal and regulatory risks for data breaches (27
May 2016) <
http://clydeco.com/uploads/Files/Emerging_legal_and_regulatory_risks_for_data_breachs.pdf>.
7. Generally undertaken at the start of the matter to put in place
proper privilege and document record management to reduce or limit
future exposure.
Download - What Are The Financial Exposures For Organisations Following Australia's Data Notification Law?
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.
[View Source]

