Originally published in the Technology Assurance & Advisory – April 2006
Executive Summary
Identity fraud is increasing dramatically. And that is just the reported cases. APACS, the UK payments organisation, reports that the cost of online banking fraud more than doubled in the first six months of 2005 compared to the same period in 20041. Similarly, ‘card not present’ fraud via the internet, phone or mail order swelled by 29% in the same period. In fact, internet fraud is said to account for a quarter of all losses.
Bad press
Security of customer information increasingly makes the headlines. There has been a raft of recent examples. These include revelations that Britain’s top-selling tabloid was able to buy confidential customer data from a bank’s call centre staff in India, reports of an attempted theft of £220m using keystroke loggers from Sumitomo bank, plus several stories of major financial institutions losing backup tapes containing the personal details of a large number of customers.
The worsening statistics combined with increasing media interest have caused considerable anxiety within the financial services industry.
Talk to the leaders
Deloitte interviewed APACS, the Financial Services Authority (FSA) and the leading financial services institutions headquartered in the UK. We wanted to understand the challenges that identity theft poses, how the financial services industry is responding and where the difficulties lie. Naturally we also hoped to determine some suitable remedies. The interviews were carried out by an independent research company.
Although experience of identity fraud varied across the organisations we spoke to, all our respondents highlighted common reasons for action:
- legislation – complying with expanding and yet vaguely worded regulatory and legislative requirements as well as demonstrating that the organisation is doing this;
- awareness – continually informing/educating customers, business partners and staff of the threats and the best ways of protecting against those threats especially given the expectation from customers that financial organisations will foot the bill when something goes wrong.
- protection of reputation – managing internal and public perceptions of the relative success each organisation is having in combating identity theft;
- technological advances – needing to deploy appropriate technical countermeasures to combat increasingly sophisticated techniques for identity theft such as phishing and pharming.
Opportunity in adversity?
Our interviewees consistently rated protection of reputation and brand as more important than defending themselves against direct financial loss and some saw protection against identity theft as a commercial opportunity to differentiate themselves from their competitors. For example, some thought this could be achieved by offering fraud insurance or advanced authentication (which provides customers with a high degree of confidence that they are not viewing a spoofed website).
People are the key
Organisations have adopted several different approaches to combat the threat of fraud through identity theft. Although the majority did not believe that technology, (such as tokens to provide two-factor authentication), was the chief solution to the problem. The consensus behind this attitude was that often it was a case of people or processes, not technology, that were the lowest common denominator in identity theft as emphasised by the targeting of call centre staff by criminal gangs.
Calling for back up
Many respondents suggested that greater legislation would be beneficial as this would help to establish a common best-practice approach. Others felt that best practice was an artificial concept and that it was up to all organisations to conduct their own risk assessments to determine the best approach for their individual circumstances.
The organisations interviewed highlighted three main difficulties:
- managing identity across boundaries – the sheer volume of users (internal and external), applications, roles, business units and partner organisations provides a very significant data challenge;
- best practice – the general lack of consensus about what constitutes best practice, in terms of protecting against and responding to identity theft means that inevitably some organisations fall behind; and
- simplicity versus security – the underlying friction between businesses and customers who want systems that are easy to use and security teams who want to maintain appropriate security controls can be problematic.
Management buys in
Interestingly, lack of senior management acceptance of this topic as a business issue, which has long been a major problem in all areas of information security, did not receive a single mention. A reflection of the increasing levels of board attention that these issues are now demanding. In fact investment is on the increase with one organisation indicating that 35% of its security budget in its current financial year was focused on tackling identity theft.
Plenty still to do
One surprising result of the research is that although all organisations were mindful of the importance of identity management and improving their authentication mechanisms – some admitted that they still had significant work to do in these areas. This was in stark contrast to the general level of confidence in their controls where the clear majority of organisations considered themselves to be either on a par with or ahead of their peers. The conclusion must therefore be the industry as a whole needs to raise the bar.
A sophisticated problem demands an equally sophisticated response
The feedback was consistent, more than ever, financial institutions are facing a wide and varied array of advanced attempts to perpetrate fraud. Although many organisations have already expended significant efforts to establish appropriate controls for validating customers’ identities, these systems need to be bolstered by sustainable compliance and monitoring mechanisms. The imperative must be to maintain high levels of protection and to quickly spot potential cases of fraud. Also, customers’ widely-held perceptions that businesses will protect them are not likely to disappear in the short term. Financial institutions need to do a better job of confirming themselves to customers and educating customers about their responsibilities and the consequences of failure.
As time goes on, the minimum level of protection required to defend your organisation and to satisfy legislative requirements is rising. Failure to keep pace may result in tougher legislation, or even litigation as customers challenge the measures in place and if they reflect "best practice" to safeguard their information.
Those organisations who can keep pace will stand out as market leaders. So perhaps this is best seen as an opportunity for security to be a differentiator rather than an inhibitor to business. But a joined up technology, people, process and business response is essential. Time will tell, but one thing is certain – Identity theft is a serious problem and one which isn’t likely to disappear soon.
We would like to thank all those who participated in the research for their time and thoughts in helping us to answer these questions.
Nature And Scale Of The Problem
Identity fraud occurs when an individual or group uses a person’s or company’s identity details, without their consent or knowledge, to obtain goods or services by deception. Attackers will target the weakest link in the protection strategy. This will either be some aspect of the internal security of the organisation or the unaware customer. As businesses become increasingly reliant on third party suppliers and service providers, and technological advancements continue to drive the way in which different parties communicate with each other; so fraud is becoming better organised, harder to detect and more ambitious. Financial institutions are one of the primary targets. Furthermore, customers are often unaware of the dangers of certain online activitiy, and place themselves in unnecessary danger of identy theft. As one institution put it – "it’s a cat and mouse game where the big organisations are now the mouse and organised crime is the cat".
Complexity of operating models
Part of the problem with internal organisational security stems from the increasingly complicated nature of operating models in many financial institutions. Outsourcing in particular stands out as a major trend which brings with it a number of risks as an organisation loses direct control over parts of its IT systems and data. In the organisations interviewed, the majority of outsourcing agreements contained detailed security provisions and the most sensitive business functions were not outsourced, but as one interviewee put it: "… there is always the people factor. It is more difficult to influence outsourced suppliers regarding their own processes". The FSA concurred – "Essentially, some firms are not taking responsibility for security within the outsourced entity … some firms don’t have a clue as to what outsourced firms are doing." Identity theft risks from outsourcing are compounded where the outsource service is offshored as differing legal and regulatory systems and business standards, combined with geographical separation, make regular monitoring of controls much harder.
Counting the cost
According to APACS, the UK’s payments association, internet, phone and mail order fraud (collectively known as Card Not Present (CNP) fraud) rose by 29% in the first half of 2005 to £90.6m2. The internet element of this was up 5% at £58m. Online banking losses increased substantially, totalling £14.5m in the six months to the end of June 2005, amounting to more than a 250% increase on the £4m for the same period in 2004. Commenting on these figures, APACS noted that "[b]oth online card fraud losses and online banking losses have grown hand-in-hand with the number of internet users and huge volumes of online card and banking transactions".
Unsurprisingly Chief Information Security Officers (CISOs) were unwilling to disclose specific figures on losses due to identity theft although one organisation admitted that this accounted for 40% of total fraud losses. However most indicated that they had recently experienced a significant number of identity theft related incidents perpetrated by both third parties and insiders, including:
ID theft related incidents
|
External incidents |
Internal incidents |
|
|
|
|
|
|
These incidents occurred despite significant amounts spent on deploying technical and procedural controls to combat identity fraud (ranging from 2% to 35% of security budgets). This may only reflect the tip of the iceberg given the inherent difficulty in detecting fraudulent activities. No wonder then that the vast majority of respondents classified identity theft as ‘a serious long term threat which will require substantial additional resources and management attention.’
Media spotlight
All of this comes at a time when media attention is particularly focused on high-tech crimes and protection of personal information – to the point where undercover reporters actively test controls themselves in an effort to detect weaknesses. The Sun newspaper, for example, was reportedly able to purchase personal information on 1,000 account holders of major UK retail banks from a call centre agent in India including addresses, passwords, credit card details and passport information. The reporter was promised details of a further 1,000 people a month from various call centres in India.
The money involved in orchestrated crime involving identity theft also makes these stories newsworthy. For example, three employees of a company providing outsourced services for a major US banking organisation stole the details of four customers and proceeded to withdraw $300,000 from these accounts.
With stories of criminals making away with billions of pounds per year and with identity theft affecting millions of people globally, these tales definitly newsworthy.
Customers are increasingly calling upon companies to make security breaches public knowledge, and there are also moves to make this a legislative requirement, as can be seen in California3. This is not surprising given that of those serious breach notifications reported since the introduction of the Californian state law in 2003, the average number of people affected per breach has been 165,000. However, this is far less than the nearly 4 million customers whose unencrypted transaction histories on closed and open accounts were compromised when a major American bank lost one of it’s backup tapes. And both of these examples pale in comparison to the estimated 40 million credit card accounts impacted by a US payments organisation security breach.
Drivers For Action
In spite of recent incidents, it is clear that organisations are recognising the problem of identity theft, and are taking actions to combat it. The organisations interviewed identified four primary factors driving their response: legislation, protection of reputation, technological advances and awareness.
Legislation
There is no shortage of local and international legislation laying out requirements and recommendations for controls to protect customer details and other sensitive information. These include the Data Protection Act, the Banking Code of Practice, FSA regulations, Sarbanes-Oxley, Basel II and the Markets in Financial Instruments Directive (MiFID). However, despite the volume of requirements, many interviewees felt that the clauses are too vague, leaving a considerable degree of interpretation up to businesses, and failing to address the specific area of protecting customer information.
APACs and the FSA are clearly concerned that financial services organisations maybe failing to fully grasp the regulatory requirements placed on them. However the latter suggested that there was an intention to leave some flexibility in the rules – "Some regulators are prescriptive, some of the EU for example. Our policy people tend to pitch it at a higher level, stating principles and allowing for interpretation". This apparent freedom was welcomed by some but others would favour an approach centering on discussion between regulators and business, resulting in a clearly defined but consensual agreement on requirements. "We would welcome a proper discussion with regulators. There’s a difference between regulatory intervention and discussion. We have to come to a consensual agreement".
Protection of reputation
Unsurprisingly, all participants saw protecting the organisation’s reputation as absolutely fundamental to success in the financial services industry. Compliance with legislation was a major factor in this.
However, two participants acknowledged that identity theft also represents a commercial opportunity to differentiate themselves from their competitors.
The United States leads the way in both the number of people impacted by identity theft and new techniques being deployed to enhance protection and in particular reputation with customers. For example, one major US bank has adopted a new mechanism to help to combat the problem of phishing. Once a user has authenticated themselves to the online banking website, they are presented with a unique image and phrase – both chosen as part of the registration process. Phishers are thwarted as their spoof websites are not able to display the customised pages for each user. Not only is this a simple mechanism from a technical perspective but it is a very unobtrusive addition to the log-on process. The security of the tool is also fortified with mutual multi-factor authentication, transparent to the user.
Other organisations have opted for more sophisticated options such as providing users with a unique token that displays randomlygenerated numbers. When that user logs on, they check that the number presented on the website matches the one on the token to confirm that they are looking at the ‘real’ website and not a spoof.
In our opinion as long as the measures deployed do not have too great an impact on usability, the vast majority of customers will welcome them as long as they improve the security of their accounts. Furthermore, as these controls become more widespread, customers are more likely to look for them when selecting who to conduct their business with.
Technological advances
In the words of one interviewee – "the pace of technological change is phenomenal". Attack techniques have evolved from simple exploitation of un-patched web server vulnerabilities with the aim of defacing a website to sophisticated blended attacks with the aim of gaining access to thousands of bank accounts in order to withdraw funds. As the perpetrators of cyber-crime have become more organised, with greater resources at their disposal, so organisations have had to become swifter at responding to each new threat. Far from it being a case of keeping one step ahead of the criminals, many companies are actually struggling to keep pace.
This is particularly so when business units demand evidence of failings before financially committing to security enhancements.
The increasing variety of technical countermeasures coming on to the market also shows no signs of slowing, although the CISOs interviewed remain unconvinced about the benefits that many of these solutions confer. The use of two-factor authentication (typically a password as the first factor combined with a token providing the user with a one-time password [OTP] as the second factor) was selected as the most popular technology to address identity theft. Most have already deployed it for privileged access to business critical systems and/or where the security risks are greater (e.g. remote access for staff). Some also saw this as the inevitable standard for the future:
However two-factor authentication is a broad term covering a wide range of techniques including different types of physical tokens (e.g. OTP, challenge-response) and biometrics (e.g. fingerprints, hand geometry, voice pattern, retina pattern, iris pattern, signature dynamics). And even though costs for such solutions are decreasing as economies of scale kick in, the fundamental problem remains that users will not want to hold several tokens from different organisations. Users already find it inconvenient to remember dozens of different passwords for their existing online accounts4.
Awareness
Whilst technological change continues unabated, with this change comes the associated need to ensure that all parties, internal and external, understand the changing nature of security problems and what their responsibilities are.
According to APACS, "millions of consumers are not even aware of some of the basic online pitfalls". This was echoed by several of the interviewees who felt that they should be investing much more in educating their customers. Issues of concern include not just the importance of installing anti-virus, firewall and anti-spyware software on home computers but also broader matters such as phishing, how to check whether a website is secure and why it is important to log out. If consumers do not understand the problem, they will not welcome complicated protection measures, believing them to be unnecessary and/or wasteful. This situation is compounded by the fact that customers are not worried because they feel that their banks will reimburse them for any loss due to identity theft. Although this may be close to the truth in the short term, inevitably there must come a point where organisations cannot accept responsibility for extreme cases of customer carelessness.
Internally, security awareness continues to be a key element within many organisations’ information security change programmes, but worrying signs remain about apparent disregard for simple security principles. One interviewee noted that staff just do not see the sharing of log-in details as comparable to giving someone the keys to their front door. Another noted that there was a big challenge in trying to convince the business that security is not always an option – in many cases it is a requirement.
What Is Industry Doing?
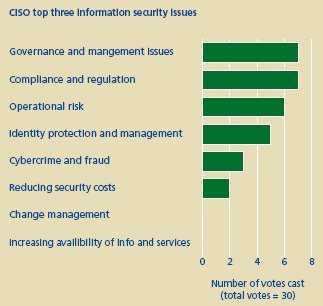
As identity theft starts to have a significant impact upon profit and brand, budgets for security generally have increased due to legislative pressure on good risk management. There were four top areas where the organisations interviewed were focusing their efforts: governance, sustainable compliance, operational risk and identity management.
Governance and sustainable compliance
The top two issues were the related areas of governance and sustainable compliance. Despite team sizes ranging from 3 to 200, information security governance was still seen by our respondents as fundamental to any organisation’s ability to deal with the threat of identity theft. The focus on information security governance mirrors the strong emphasis currently placed on organisations having a robust IT governance model. It also enables the two governance structures to dovetail, providing better integration across the various teams and a simpler operational model for running the business.
Information security compliance is no longer seen as a one-off, ad-hoc activity to be conducted solely by business units themselves; organisations are now seeing the need to conduct compliance assessments according to a regular, scheduled timetable. They are recognising the advantage of automated monitoring and building compliance metrics in to systems and solutions from the beginning. From an identity theft viewpoint, this is a major step towards identifying weaknesses and failings as well as detecting possible abuses.
Operational risk
One organisation summed up their approach to risk analysis very simply – "We don’t do anything without a risk analysis …." All interviewees shared the focus of having clearly defined risk/threat assessment methodologies, combined with straight-forward cost/benefit analysis to determine the appropriate response to each risk/threat. They also typically managed risk across three areas – market, credit and operational risks – with identity theft falling predominantly into the latter category. However there was an acknowledgement that risk is not easily quantified – "Reputational risk is very important but very difficult to quantify as it doesn’t necessarily translate into fall-off in banking or internet banking usage". Also one organisation noted that it was difficult to implement one rigid risk methodology for the whole organisation due to differing views on what to measure – "A formal risk analysis is difficult … there is no group-wide view".
Identity management
Half of the organisations interviewed had major identity management projects supported by a range of business drivers:
- business facilitation – the need to do business regardless of location and type of end-user (e.g. customer, supplier, employee);
- cost containment – reducing/avoiding staff overheads combined with the ability to push costs to partners;
- operational efficiency – increasing standardisation such that employee productivity and user convenience increases;
- risk management – internet-based solutions exposing more sensitive content and services ensuring internal people had access to the right things and ensuring this was revoked when it was no longer needed i.e. more secure internal systems;
- regulatory compliance – ensuring compliance with Sarbanes-Oxley, GLBA, CA SB 1386, HIPAA, FERC/NERC, etc.
Some of those organisations were deploying reasonably simple solutions, at least in the short-term, for example consolidating users and roles into one authoritative source but not introducing singlesign- on or user provisioning. However, it is clearly a significant step towards being able to better manage access to systems with associated audit trails.
Why Is It Difficult?
Although historically senior management buy-in was always a significant hurdle for security teams to overcome, this issue was not mentioned once in interviews. However, organisations highlighted a number of other difficulties: managing internal identity across boundaries, the search for elusive best practice and the conflict between simplicity and security.
Managing identity across boundaries
The sheer volume of users, customers, applications, roles, business units and partner organisations provides a major challenge to organisations that historically may not have been particularly proactive in closing down internal access to systems.
In other words users need access to do their job. Unfortunately this makes abuse easier too. Proving that an account is no longer required, or has excessive privileges can be very difficult and well intentioned but erroneous reductions in access rights can have significant business repercussions. It may even be difficult to identify the true business owner of legacy applications making the task even harder. Even where role-based access has been achieved and identities are federated – allowing interoperability across companies and networks – it is still a major challenge to maintain this. Getting it right involves a major programme of work and a number of interviewees admitted that there was still significant work to do. Something of a contrast to the general level of confidence the participants had in their controls.
Best practice
The CISOs were divided on whether there is such a thing as best practice when it comes to addressing identity fraud in the financial services industry. Although most expressed a desire to reach a greater consensus on the terms and definitions used. The financial institutions felt that the FSA and APACS could play a major part in building this consensus and providing more guidance.
Some also were of the opinion that greater collaboration between organisations would help. Although given the potential impact on reputation, there is an understandable reluctance to share information. It is clear that staff vetting, segregation of duties, leastprivilege access, regular penetration testing, role-based access and secure authentication are all good general information security principles. However, in the absence of such advice, the main focus should be in determining the right approach for each situation through the use of risk assessments, cost/benefit analysis and the building of business cases.
Simplicity or security
The underlying conflict between having simple processes for customers, employees and business partners, and maintaining appropriate security controls to protect the confidentiality, integrity and availability of information has long been a problem for senior management. For example businesses have been less than enthusiastic in deploying token-based, two-factor authentication solutions.
However, information security teams must continue to develop their abilities in assessing the suitability of solutions and building business cases to support the key initiatives that will provide significant benefits to the organisation.
This is an area where opportunities to take a lead as a business may allow security to shake off some of the negative connotations it has had. The use of new authentication methods could be a differentiator in a mature, highly competitive market.
What Is The Way Forward?
There is no single or simple solution to the problem of identity fraud. Organisations large and small across all areas of financial services have to face a constantly evolving set of techniques making use of sophisticated technologies and social engineering methods. A few messages did crystallise as a result of our research.
Getting the fundamentals right
The first and arguably most important message that came out of our research was that organisations aren’t always succeeding in addressing the fundamental problems that they still need to address. Closing down redundant accounts, ensuring that internal users have the least privileges required to do their jobs and ensuring that password reset processes are secure; these are all simple and longestablished best practice principles. But few organisations can quickly prove 100% conformance to them. As one organisation put it, the first step in tackling identity theft was "getting the basic data and processes right first, followed by progress towards stronger identification". Another noted that they looked for advisors who "… have practical experience of data and process issues first, and technology second".
There is also a need to ensure that the controls deployed are bolstered by robust compliance and monitoring mechanisms, ensuring consistently high levels of protection, thus quickly spotting potential cases of fraud.
Education
Many organisations do have security awareness systems or projects in place, but there is still much to be done. The general focus on raising internal awareness does not tackle the customer-facing issues. Internally, organisations should move from the distribution of HR-acceptable usage policies and high-level security awareness intranet sites, and adopt a three-point approach:
- detailed security training for key groups of users (e.g. Help Desk, administrators, backup teams);
- online tests for all new employees and contractors to ensure they understand their information security responsibilities (and the consequences of not meeting those responsibilities); and
- regular awareness campaigns to keep the key messages in people’s minds.
Organisations should take every opportunity to keep customers abreast of the latest identity theft techniques and sources of information (e.g. www.identity-theft.org.uk).
The education of other external parties should also receive more attention. Organisations should regularly assess outsourcing organisations to ensure their employees can demonstrate a sound understanding of information security principles.
Technology
Although technology was not seen as any kind of cure-all by the CISOs interviewed, they all accepted that it will play a very significant part in the future. One CISO saw his main objective for the next twelve months as "finding better tools to prevent fraud and identity theft, with the least complicated solution for the customer."
In terms of technical solutions for identity theft, two-factor authentication provided by the use of tokens was the clear leader with all participants. Two-factor authentication through biometrics, on the other hand, was only chosen by four of the CISOs.
However, in tackling the internal threat, the responses centred on just a few areas where technical solutions help: consolidating accounts, providing role-based access and strengthening how the user authenticates themselves to the organisation. For example no respondents highlighted Enterprise Single-Sign-On (eSSO) solutions, although such solutions not only provide the opportunity to raise the bar for security but can also provide cost savings and improve usability; thereby gaining support from the business and marketing. User provisioning is another area which nobody mentioned, and yet it often provides a compelling business case.
Authentication should not just be limited to improving the way that customers prove themselves to organisations but also how organisations prove themselves to customers. Too often SSL/TLS is seen as the right solution for both confidentiality and authenticity but the reality is that many users do not understand how this technology works and what to look for. Easily understood customised online login procedures combined with transparent two-factor authentification is one solution to this. (See page 5 for the unique image/phrase solution adopted by one American bank.) This tactic not only increases security for users as they see something personal and obvious to confirm they are looking at the right site, but it also helps build a user’s personal experience. This has long been a problem with the adoption of online services.
There are also out-of-band mechanisms that can not only enhance security but also enrich the customer experience. For example, the inputting of a valid username and password can trigger an automated telephone response to the customer’s mobile phone, or the sending of a SMS message to the mobile phone containing an OTP.
Moving away from the more obvious solutions may pay more dividends as well as being a key differentiator in what are often established and relatively stagnant markets.
Conclusion
The scale and frequency of identity theft is set to increase and the resultant fraud poses a real threat to e-commerce in particular. Financial services currently bear the brunt of the onslaught as organised crime begins to realise how lucrative identity theft can be. At the same time customers are shying away from online business services which many see as a convenient but inherently dangerous way of conducting financial transactions. Therefore the question is not whether identity fraud will be perpetrated but rather which organisations will fail to keep ahead of the game and therefore suffer the consequences.
However, periods of change bring opportunities as well as challenges. Identity theft offers a chance to demonstrate how security need not be just a cost or a regulatory requirement but how it can be a true business enabler. Clearly any innovative solutions need to be coupled with a pragmatic approach to delivery. For those organisations that find the right blend then increased market share, increased productivity and reduced costs are all possible by-products of increased security.
In other words, as with any form of adversity, those organisations that can evolve with the environment will fare best in the future.
Footnotes
1 APACS report, 8 November 2005: "Latest card fraud figures show internet fraud accounts for a quarter of all losses".
2 Ibid.
3 State law AB 1386-Peace/CHAPTER 915, Stats of 2002.
4 Note that the identity card proposed by the UK Government as it currently stands, will not aid in the proper authentication between individuals/businesses.
The content of this article is intended to provide a general guide to the subject matter. Specialist advice should be sought about your specific circumstances.
